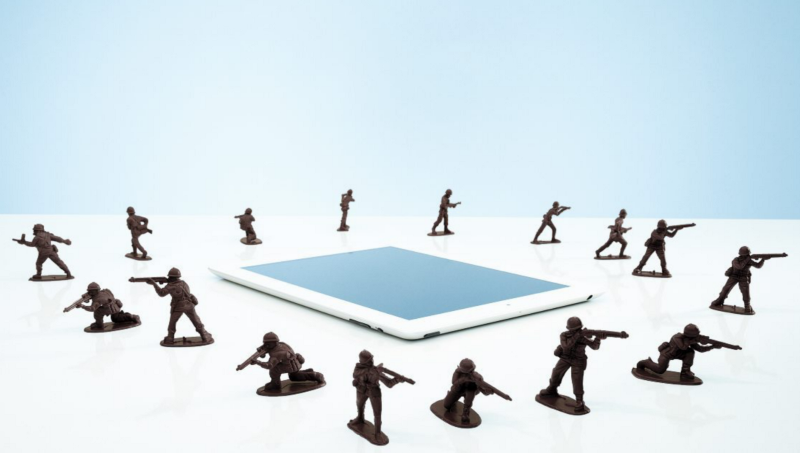
— The Forum’s new Global Centre for Cybersecurity seeks to help companies and governments better combat digital infiltrators
It’s every CEO’s nightmare. A data breach not only impacted your company, it compromised the personal information of the nearly 1.5 million people connected to your network. That is what happened to Equifax, a U.S. consumer credit reporting agency, last September. Data breaches have become a commonplace part of digital life and such outside threats, along with technology developments, leave companies more vulnerable than ever.
There are a lot of negative implications of massively scaled networking, says Adam Ghetti, founder and chief executive officer of Ionic Security, a World Economic Forum Technology Pioneer and a member of the Forum’s Global Future Council on Cybersecurity.
“Look at Equifax. A single breach at a single company can do irreversible damage to the vast majority of adults in America by compromising information that is deemed to be private and can’t be changed — you can’t go out and get another social security number or date of birth. The implications of these things have grown beyond security best practices,” he says. Indeed, cybersecurity threats are outpacing the ability of companies and governments to overcome them unless all stakeholders begin to cooperate, according to a new report by the Forum in collaboration with The Boston Consulting Group (BCG). The report covers 14 policy topics that need to be addressed. It is against this background that the Forum will officially launch its Global Centre for Cybersecurity during the annual meeting in Davos on January 23rd to 26th. “The World Economic Forum can use its unique convening ability, especially among the most senior industry decision-makers and government policymakers, to help drive real-world solutions to vexing cybersecurity challenges,” says Alan Cohn, co-chair of the Forum’s Global Future Council on Cybersecurity and a former director of Emergency Preparedness and Response Policy at the U.S. Department of Homeland Security.
A Need For Guidelines
Addressing these threats requires dialogue across industries and competencies, and on subjects from the technical to the ethical, says the report. Currently, dialogue between leaders in the public and private sectors is often off-target and at cross purposes, the report says. Policy implementation also varies by national context: every country has its own unique capabilities, vulnerabilities and priorities.
Companies also need guidelines as they are constantly sharing sensitive data and interconnecting with vendors and business partners, opening themselves to tremendous vulnerabilities. “It has gotten so bad that I know of $100 million contracts that have been held up for a year or more while the buyer and seller negotiates what type of warranties to provide for sensitive data,” says James Kaplan, who leads McKinsey’s Infrastructure and Cybersecurity practice. “There are no standards so everything is a bespoke negotiation.” Technology developments and the rate of change are escalating concerns. “We are beyond human scale defense,” says Ghetti of Ionic Security. “We have so many systems that are implemented by so many different stakeholders that there is not a single group of humans capable of wrapping their heads around all of the problems all of the time.”
That is where artificial intelligence can help. “We need to figure out how to get the systems themselves to take part in the active defense,” says Ghetti. “What I mean is that we have to rely more on the machines themselves not just to tell us that there is something suspicious. We need the machines to do something about it before a human can respond.”
But technology is a two-edged sword. Artificial intelligence will play an increasingly large role on both sides, underpinning much more capable defense but also enabling increasingly sophisticated cyber attacks. Today, it takes a lot of time and money for criminals to find vulnerabilities in software programs or networks and exploit them. With AI the process of detecting flaws will be automated. So instead of looking for a tedious needle in the haystack, the bad guys could start launching frequent “zero day attacks” that target publicly known but still unpatched vulnerabilities.
Vulnerable To Attack
The introduction of a quantum computing could also cause headaches. It has the potential to disrupt the use of encryption, a critical piece of data security and protection against threats. So, the forum advises companies and governments to prepare because existing methods of computationally based encryption may soon no longer guarantees protection of data. Luckily, there are other types of encryption currency being designed and tested that are not subject to the same decryption risks from quantum computing, and there are other approaches to data and system protection besides encryption, says a Forum cybersecurity report. The way networks are currently structured also exposes companies to attacks .
Open innovation models, which encourage businesses to bring in external ideas and technologies, and the introduction of the Internet of Things (IoT) — the name given for the interconnection via the Internet of computing devices embedded in everyday objects, enabling them to send and receive data — are also compounding cyber-security issues.
Collaboration is Key
Different technologies and technology protocols, including those that use blockchain to allow individuals to retain control of personally identifiable information, that let devices more securely authenticate onto networks, and that distribute and synchronize ledgers across several (if not hundreds, or thousands) of computers, may be better platforms for constructing more secure and resilient information and data networks, according to a Forum report.
Blockchain technology, the technology that underpins cryptocurrencies like bitcoin, holds the potential to serve as this new type of distributed, decentralized platform. Features like identity verification and validation, device authentication, and secure ledger keeping, may be better suited to resisting cyber threats. Nonetheless, critical infrastructure, whether owned by the public or private sector, may increasingly find itself on the front lines of cyber-conflict, no longer seen as civilian infrastructure but rather as a legitimate target in conflicts between states, or within states, according to a Forum report.
All of these things make it more important than ever for stakeholders to collaborate on defense. For example, an effective intelligence-sharing policy will help limit the spread of malicious software, and the greater adoption of encryption may limit the ability to monitor and police network traffic, says the Forum report. In practice, what this means for business leaders and policymakers is that cybersecurity policy-making efforts should be more collaborative and deliberative. Efforts should also be framed in the context of an ongoing iterative process rather than ad-hoc and crisis-driven, resulting in patchwork legislation, the report says. Ghetti agrees. “What we have today is a surface level of collaboration but we have a very deep set of challenges. What we need is authentic collaboration.”






